Password in application.properties?
Secure with your Spring Boot application with Jasypt
Microservice architecture necessarily means that your service will communicate with other services. In most cases, this will also require some kind of authentication. In spite of all the advances in encryption and authentication algorithms, and obvious disadvantages of shared secret based authentication, most of us continue to use a shared a username/password to authenticate each other. Well you can't change the world around you. So your service has to use it as well! Any sensible developer with make sure that such passwords are not hardcoded in the Java code. But then the question remains unanswered - where should it go? The properties file is the next best place. But, it is not good to have the passwords saved in plain text. Many from the IT Support team have access to the application.properties file. How do you guard the passwords from any spying eyes?
Jasypt
Java Simplified Encryption is a useful utility for doing this. It can help us encrypt passwords before saving to the properties file. Such encrypted password is seamlessly decrypted before use in the code. So it is light on either side. Ofcourse, this mechanism is not 100% secure. What can be decrypted by the application code can be decrypted by any utility code written by a hacker. So anybody having access to the property file and the encryption key, will be able to get the password. But, now it is a multi step process. Hence, a little better than having bare passwords in the property file. Let us see a simple implementation of Jasypt.
Maven Dependency
Of course, the first step is to add the required maven dependency.
<!-- https://mvnrepository.com/artifact/com.github.ulisesbocchio/jasypt-spring-boot-starter -->
<dependency>
<groupId>com.github.ulisesbocchio</groupId>
<artifactId>jasypt-spring-boot-starter</artifactId>
<version>2.0.0</version>
</dependency>
Annotation
Next, we add the @EnableEncryptableProperties annotation to the main configuration class. This announces to Spring Boot that we are going to use encrypted properties in our application.
@EnableEncryptableProperties
public class Application {
}
Encrypt the passwords
We need to encrypt the passwords before saving them into the properties file. This can be done on CLI with the Jasypt Jar. Note that we need a secret key for encrypting the password, and the same is used for decrypting it.
java -cp //jasypt-1.9.3/lib/jasypt-1.9.3.jar org.jasypt.intf.cli.JasyptPBEStringEncryptionCLI input=”A@Strong#Password@#$1245″ password=secretkey algorithm=PBEWithMD5AndDES
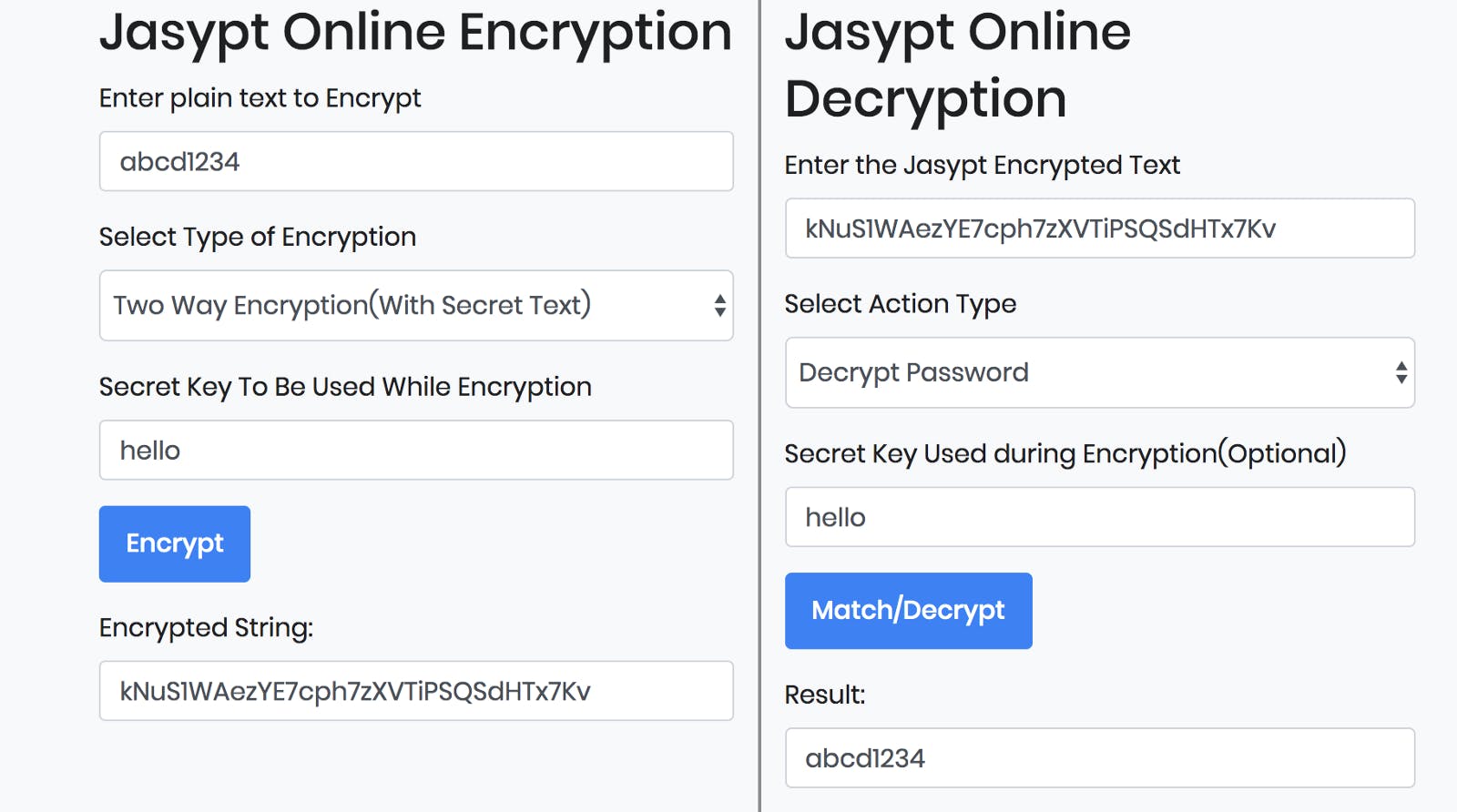
If you don't like CLI, you can also use some of the online utilities to do the same job. It has a clean UI interface that does the same job behind the scene.
Such encrypted passwords have to be added to the properties file with a special syntax - so that Jasypt will seamlessly decrypt them for you. A typical password would look like this:
db_uid: admin
db_password: ENC(sdfsda/234GFSDGDFGDasf)
Provide Encryption Key at Runtime
Well, I don't like this. But, we have to accept that password authentication can never be 100% secure. We encrypt the passwords before saving to the property file - so that nobody can see the real password. But the encryption key has to be passed into the application - using a command line option. So, anybody with access to both will be able to decrypt the password. But this adds a layer of protection, letting us reduce the risk.
There are two ways to feed the secret key into a running application.
- Command Line Option
-Djasypt.encryptor.password=secretKey
- Environment Variable
JASYPT_ENCRYPTOR_PASSWORD=secretKey

